We’ve mentioned before that you can install Linux on a computer that can’t run Windows 11 as an alternative to buying a new computer. Here we’re going to go into more detail about that option. With Windows 10 having reached its end of life, it’s increasingly unsafe to keep using it, as unsupported software is […]
Category: News
Have I Been Pwned?
Worried about the security of your accounts? A quick and easy way to check if your account details have been compromised and leaked online is to check through the website Have I Been Pwned. While it might seem strangely named, due to the use of gaming slang, it is a genuinely useful security tool. Simply […]
Windows 10 Extended Security Updates now free in the UK
Good news for Windows 10 users in the UK: Microsoft is offering Extended Security Updates (ESU) to help keep your device secure now that official support for Windows 10 has ended as of 14th October 2025. While ESU was originally going to cost a one-time fee of £24.99, it’s now possible to enrol for free […]
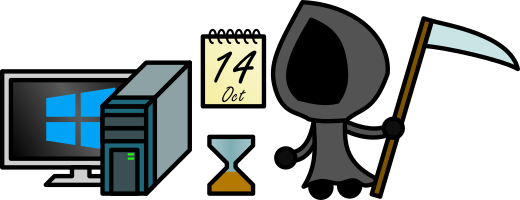
Windows 10 Has Reached End of Life. Here’s What That Means for You
As of today, Windows 10 has officially reached its end of life. Your computer won’t suddenly stop working, but continuing to use Windows 10 from this point forward comes with serious risks. Here’s what you need to know, and why it’s important to act quickly. ❌ No More Support or Updates Microsoft has officially ended […]
Windows 10 Is Nearing End of Life: Here’s What You Need to Know
If you’re still using Windows 10, it’s time to start planning your next steps. Microsoft will officially end support for Windows 10 on 14th October 2025, just one month from now. On the surface, this might not sound like an important issue, but it has serious implications for your device’s security and reliability. Why This Matters […]
Beware the Gift Card Scam
Why Being Asked to Pay with a Gift Card Is a Major Scam Warning Scams come in many forms, but there are a few common warning signs that can help you spot them early. One of the biggest is being asked to pay with a gift card. At first, it might seem odd; why would someone […]
Windows 10 End of Life: More Options Available
Are you still using Windows 10? With Microsoft officially ending support on October 14, 2025, time is running out to upgrade to a supported operating system. But if your PC can’t handle Windows 11, don’t panic, there’s a safety net. Windows 10 Extended Security Updates (ESU) Program The Extended Security Updates (ESU) program is Microsoft’s […]
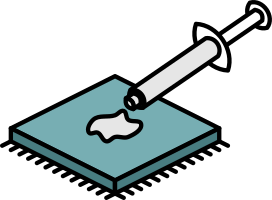
Thermal Paste Reminder
Replacing Thermal Paste in Your Computer: Why and How When was the last time you replaced the thermal paste in your computer? It’s crucial to monitor your computer’s temperature, especially during the summer, as excessive heat impairs its performance. Dust inside the casing is a common cause of overheating and cleaning it is a good […]
Cleaning a Desktop Computer
The sheer amount of dust that can get inside a computer can be surprising. Dusting inside your computer is crucial for maintaining its performance and longevity. Dust accumulation causes overheating, leading to reduced performance and hardware failure. Here’s a step-by-step guide to help you dust your computer safely. Why Dusting is Important Prevents Overheating: Dust […]
Overheating
Is your computer struggling with the heat? Overheating can cause a computer to slow down or even shut down entirely. Fortunately, there are several strategies you can employ to keep your computer cool, ranging from simple adjustments to more involved solutions. External Solutions Ensure Proper Airflow: One of the easiest ways to prevent overheating is […]