Worried about the security of your accounts? A quick and easy way to check if your account details have been compromised and leaked online is to check through the website Have I Been Pwned. While it might seem strangely named, due to the use of gaming slang, it is a genuinely useful security tool. Simply […]
Category: Security
Windows 10 Extended Security Updates now free in the UK
Good news for Windows 10 users in the UK: Microsoft is offering Extended Security Updates (ESU) to help keep your device secure now that official support for Windows 10 has ended as of 14th October 2025. While ESU was originally going to cost a one-time fee of £24.99, it’s now possible to enrol for free […]
Windows 10 Is Nearing End of Life: Here’s What You Need to Know
If you’re still using Windows 10, it’s time to start planning your next steps. Microsoft will officially end support for Windows 10 on 14th October 2025, just one month from now. On the surface, this might not sound like an important issue, but it has serious implications for your device’s security and reliability. Why This Matters […]
Beware the Gift Card Scam
Why Being Asked to Pay with a Gift Card Is a Major Scam Warning Scams come in many forms, but there are a few common warning signs that can help you spot them early. One of the biggest is being asked to pay with a gift card. At first, it might seem odd; why would someone […]
Windows 10 End of Life: More Options Available
Are you still using Windows 10? With Microsoft officially ending support on October 14, 2025, time is running out to upgrade to a supported operating system. But if your PC can’t handle Windows 11, don’t panic, there’s a safety net. Windows 10 Extended Security Updates (ESU) Program The Extended Security Updates (ESU) program is Microsoft’s […]
What Should You Do With a Lost USB Stick?
Why You Should Never Plug in a USB Stick You Found Finding a USB stick on the ground might feel like stumbling upon a mystery waiting to be solved, but before you plug it into your computer out of curiosity, stop. That small device could be hiding a big risk. The Hidden Dangers of Unknown […]
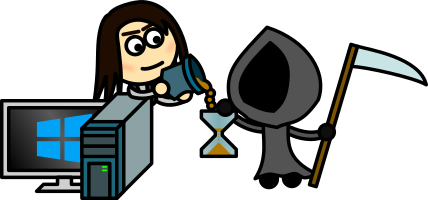
Phishing vs. Two-Factor Authentication
Recently, a friend shared that she received a phone call from someone claiming to be from her bank, requesting access codes from her authentication app. It turned out to be a scam aimed at gaining access to her bank account. Phishing Scams Phishing is a common scam where a malicious user tries to gain access […]
Windows 10 End of Life: Six Months Remaining
Are you still using Windows 10? The Clock is Ticking Windows 10 will reach its end of life in just six months. It will continue to receive updates until then, but official support will cease after that point. This might sound appealing if you’ve ever been interrupted by an untimely update, but the risks are […]
The Importance of Locking Your Computer
Locking the Computer Environments such as libraries, offices, or shops, where your computer might be accessible to the public or unauthorised individuals pose an often-overlooked security risk: someone else using your computer while it’s logged in as you. This can have significant consequences. Potential Risks Minor Mischief: On the less dangerous side, someone might post […]
Using Password Managers To Keep Your Password Secure
Do You Reuse Passwords? In today’s digital age, the security of our online accounts is paramount. General security guidelines strongly advise against reusing passwords across multiple accounts. The reason is simple: if one login is compromised, it could potentially grant access to all other accounts using the same password. However, remembering a unique password for […]